Page 24 - SCR-Lloyds-CFPA-Table Ronde-Presentation
P. 24
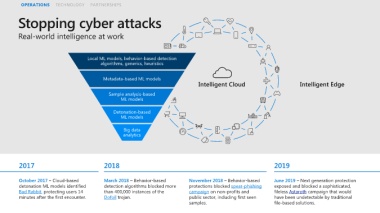
OPERATIONS TECHNOLOGY PARTNERSHIPS
Local ML models, behavior-based detection
algorithms, generics, heuristics
Metadata-based ML models
Intelligent Cloud Intelligent Edge
Sample analysis-based
ML models
Detonation-based
ML models
Big data
analytics
2017 2018 2019
October 2017 – Cloud-based March 2018 – Behavior-based November 2018 – Behavior-based June 2019 – Next generation protection
detonation ML models identified detection algorithms blocked more protections blocked spear-phishing exposed and blocked a sophisticated,
Bad Rabbit, protecting users 14 than 400,000 instances of the campaign on non-profits and fileless Astaroth campaign that would
minutes after the first encounter. Dofoil trojan. public sector, including first seen have been undetectable by traditional
samples. file-based solutions.